Metasploit Pro 4.22.0 Crack With Registration Key Full Version 2023 Download
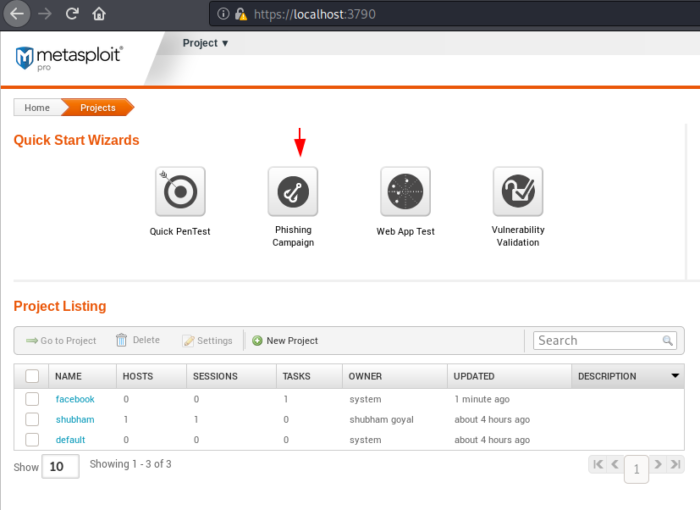
Metasploit Pro Crack is a simple and comprehensive penetration testing solution specially designed for users who want to reduce the risk of a data breach. This helps them to simulate attacks on their network in a secure environment to search for vulnerabilities. Monitor security and countermeasures, and manage and organize phishing detection. After entering the project name and destination addresses, you can easily navigate through tabs such as Analysis Setup, Launch Tools, and Generate Report to customize all of the options to suit your needs. Metasploit Pro Crack Download is a solution for security professionals in corporate and government agencies. And consultants who need to cut costs to make network security testing more efficient and effective.

It increases the efficiency of the penetration tester by providing unlimited remote access and enabling teams to collaborate effectively. The app instantly searches for vulnerabilities, threat intelligence, and quickly prioritizes any high-risk threats that require your attention. Metasploit offline activation crack is a penetration testing tool that increases the performance of penetration testing. Prioritizes and recognizes risks by checking for closed vulnerabilities and measures security awareness through fake phishing e-mails. It helps security and enterprise IT professionals prevent data leaks by effectively conducting thorough penetration testing, vulnerability prioritization, audits, and risk mitigation measures. Skills include smart usage, password management, web application analysis, and social engineering.
Metasploit Pro Crack Full Download
It is the world’s leading penetration test solution for corporate security. And advanced penetration test applications. You can test your countermeasures by securely simulating attacks on your network to discover security gaps. Used to scan for vulnerabilities as part of your vulnerability management tool. It can work on Metasploit Pro and present its results in consolidated reports. Metasploit Pro Keygen is a set of tools for using other machines. Some Metasploit offline activation crack modules use system functions to make unsafe calls because they do not validate user input. The vulnerability has no impact on the framework because anyone who remotely accesses the procedural mechanism can invoke system commands. In the community version, there is only one user, an administrator.
It can allow console access to gain direct console access and execute commands. Metasploit Pro offers a multiplayer mode, the only robust model where this conclusion is problematic. The latest version of Metasploit Pro is a commercial web interface for downloading the Metasploit full version with the crack framework. These tools provide significant automation and ease of use for new users while providing full access to the platform. Both products also offer tools that are not available in the versions of the community platform, such as automatic password enforcement and automated site attacks. Additionally, a good reporting backend for Metasploit Pro can speed up one of the less popular aspects of penetration testing: reporting.
The OMIGOD is RCE
We are thrilled to share that we have a module that addresses the OMIGOD vulnerability that exploits CVE-202021-38647 from Spencer McIntyre, our own Spencer McIntyre! If exploited, it will allow an attacker who is not authenticated to gain root level execution against the affected servers. As Metasploit product key generator has already been seen in attacks in the wild carried out through the Mirai botnet we’d love to see your servers patched in case your servers decide to join the zombie horde this Halloween!
Sophos is a part of the RCE Pile
In line with the growing trend of non-authenticated RCE exploits that permit the root code execution this week, we have an exploit for CVE-2020-25223, which is an unauthenticated RCE inside the Sophos UTM WebAdmin service. Although we haven’t yet witnessed any exploits that have been discovered in the wild due to this vulnerability, it is certainly one that needs to be patched due to its seriousness. Be warm!
Guess Who’s Back”Back Again,” Apache’s Back. Tell a friend
While it’s not a marshaling issue (I’m sorry, it’s Halloween and it’s time to make some puns) community members Ash Daulton, Dhiraj Mishra, as well as mashallah (RAMELLA Sebastien), have created scans and exploits for CVE-2021-41773 as well as CVE-2021-42013 that was developed based on research from RootUp, ProjectDiscovery, and HackerFantastic. The vulnerabilities that cause path traversal are simple to exploit and received lots of coverage in the media as it’s been quite a duration since Apache has seen a solid RCE exploit for it. This is certainly one you should be patched if you’re running Apache servers. If successful, the exploit will lead to remote code execution, as the user is running an Apache server. Apache server.
You can also download>>>NeoFinder Crack
Metasploit Pro Serial Key Features:
- Latest utilities and payloads Use the world’s largest database of quality and integrated open source and integrated applications to run tests.
- Advanced Attack Targets compromises standard and custom web applications, network devices.
- Database servers, endpoint systems, and email users.
- Full Graphical User Interface – Simplifies use and improves efficiency for penetration testers and security experts in a step-by-step model.
- VPN rotation – tunnels all traffic through a target, for example, to scan for vulnerabilities directly through a compromised computer.
- Social Engineering – Uses anti-phishing tests and endpoints to set up campaigns, track clicks, and collect passwords.
- Web Applications – Identify enterprise-wide web services, view these vulnerabilities, and quickly exploit them to validate results.
- Team Support – Allows teams to coordinate coordinated attacks.
- Reliable reports – including online and offline reports detailing vulnerabilities and fixes to custom descriptions and design templates.
- Confirming a closed-loop vulnerability gives priority to recovery.
- Therefore, you can get rid of the dynamic load with top-end antiviruses.
- Select from the Pro Console and the web interface.
- Enter details to enforce.
- Basic Overview Guide.
- Promote Sarbanes-Oxley compliance by advocating mandatory controls and procedures.
- Security, especially computer science, is often the focus of our day.
- So simulators can take the best steps to protect the integrity of your company.
- And effective modeling and functionality can help you plan the best security action plan.
What’s New in this Version 2023?
- Metasploit Pro Full Cracked can run tests to automatically obtain all the necessary information about the target network.
- You can also identify active ex-employee accounts and check for weak passwords on the network.
- Passwords can be verified in various network services including Telnet, VNC, and SSH.
- Upon completion of the test, a detailed report is generated.
- Using a Metasploit Pro activation key precompiled is a great way to provide customers with proof of concept.
- It can also be used when we get a local wrapper on a machine or RCE via a web application.
- Sometimes it is easier to create a shell to read the flipped counter than to flip the bash shell.
- Guidelines for major changes to the standard.
- Handmade brute force certificate.
- Select in the Pro Console and the web interface.
- Connect to data manually for enforcement.
- Controlling vulnerabilities with feedback is a priority when remediating vulnerabilities.
Pros:-
- Complete penetration testing tasks faster by automating repetitive tasks and leveraging layered attacks.
- Assess the security of web applications, networks and end systems, and email users.
- Substantially realistic network attacks based on the core Metasploit framework with over 120,000 users
- Collaborate more effectively with team members in coordinated network tests
- Customize content and report template
Cons:-
- Some farms require intervention to operate.
Metasploit Pro Serial Keys:
NBVC5-43WSD-F987Y-TF43W-3ESDF-8Y7T-EDFG
SDCFV-BN098-UYTR-43WS-EDFGI-UHGF4E-RFGV
DVBN-98UY-T3WES-DFGIU-JHGFD-ES4567-898UY
SXDC-VB98-7YTR-3WSE-DFG9-87YT-F43W-SEDRF
Metasploit Pro License Key:
JHGVE-SEDXC-FGVBH-JNUY-HGVS-XDCFV-GBHCF
HGVC3-WESDF-CVGBH-NJ7YTR-3WSDX-CFGVBH
YGTFE-DRFT-GHJ67-TRFD-3WSE-XDCFGV-HBYTF
JHGF3-WSD-XCFVG-HBJN8-UYTGF-WASZ-XCFGV
System Requirements:
- Microsoft Windows SP1 / XP / Vista / 7/8/10 and Server 2008 R2, 2012 R2.
- 64-bit versions of the following platforms are supported.
- 2 GHz + processor.
- 4 GB of RAM available (8 GB recommended)
- 1 GB of free disk space (50 GB recommended).
- Red Hat Enterprise Linux Server 5.10 or later.
- Ubuntu Linux 14.04 or 16.04 LTS (RECOMMENDED).
How To Install/Crack?
- First, download Metasploit Pro Crack from the provided link.
- Disable virus protection.
- Install this software as usual.
- Unpack and run the RAR file here.
- Then press the crack button and close it.
- Open Crack, copy Crack, and paste into your installation folder.
- Then activate this software.
- Done.
Download Link is Given Below…